Introduction
To update a BIOS or device firmware in Linux traditionally meant rebooting into Microsoft Windows, or preparing a MS-DOS floppy disk (!) and hoping that everything would work after the update. Periodically searching a vendor website for updates is a manual and error-prone task and not something we should ask users to do.
Is my hardware supported?
The LVFS only provides firmware once the original OEM vendor has joined the project and uploaded files themselves. The OEM vendor is in full control over what models are supported and is the only entity that can add support for new hardware. There are a large number of devices already supported and we also have a public record that explains vendor engagement with the LVFS project.
fwupd
fwupd is a simple daemon to allow session software to update device firmware on your local machine. It's designed for desktops, but also usable on phones and headless servers. You can either use a GUI software manager like GNOME Software to view and apply updates, the command-line tool or the system D-Bus interface directly. Updating firmware on Linux is now automatic, safe and reliable.
$ fwupdmgr get-devices Unifying Receiver DeviceId: 5ad59b26d556e226f9e5e1ca13e4b717fe19802c Guid: 77d843f7-682c-57e8-8e29-584f5b4f52a1 Summary: A miniaturised USB wireless receiver Plugin: unifying Flags: updatable|supported|registered Vendor: Logitech VendorId: USB:0x046D Version: RQR24.05_B0029 VersionBootloader: BOT03.01_B0008
You can see all the command line options using --help:
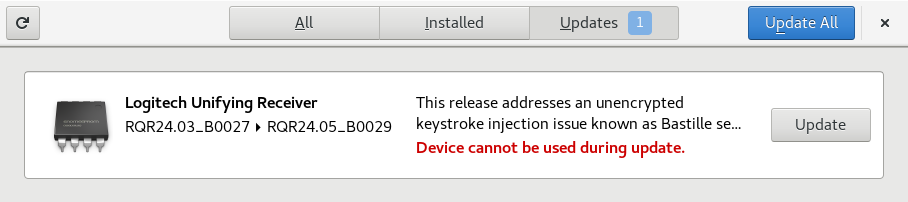
GNOME Software
GNOME Software is an application store designed to make installing, removing and updating both easy and beautiful. It is available for Linux and used by millions of people on RHEL ≥ 7.4, Fedora ≥ 22, Ubuntu ≥ 16.04 and Debian ≥ 9.
When required, metadata files are automatically downloaded from the LVFS and submitted into fwupd over D-Bus. If there are updates that need applying then they are downloaded and the user is notified and the update details are shown. The user has to explicitly agree to the firmware update action before the update is performed.
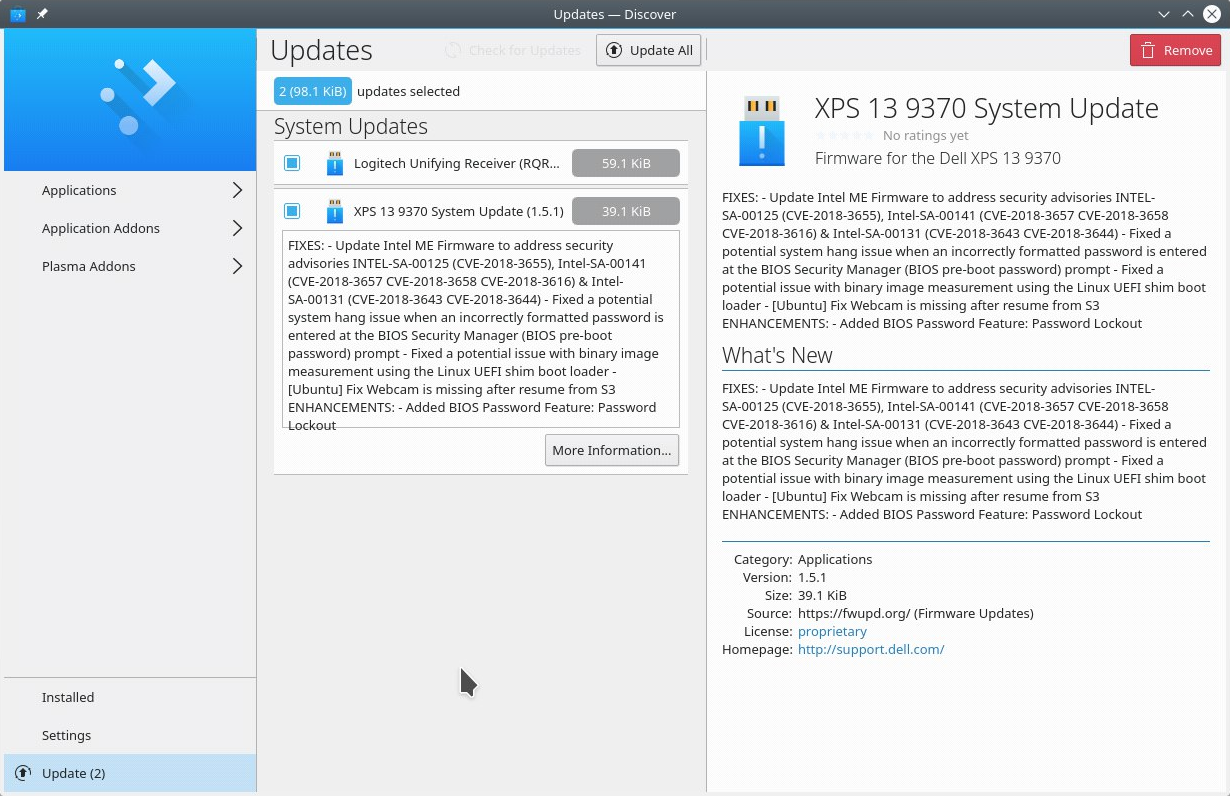
KDE Discover
Discover is intended for users and distros where the terminal isn't the optimal solution for installation of apps and add-ons or updates. It comes Pre-installled with many Linux distro's such as KDE Neon, Kubuntu and is generally bundled with KDE Plasma. Metadata files are periodically downloaded, from the LVFS and submitted into fwupd over D-Bus.
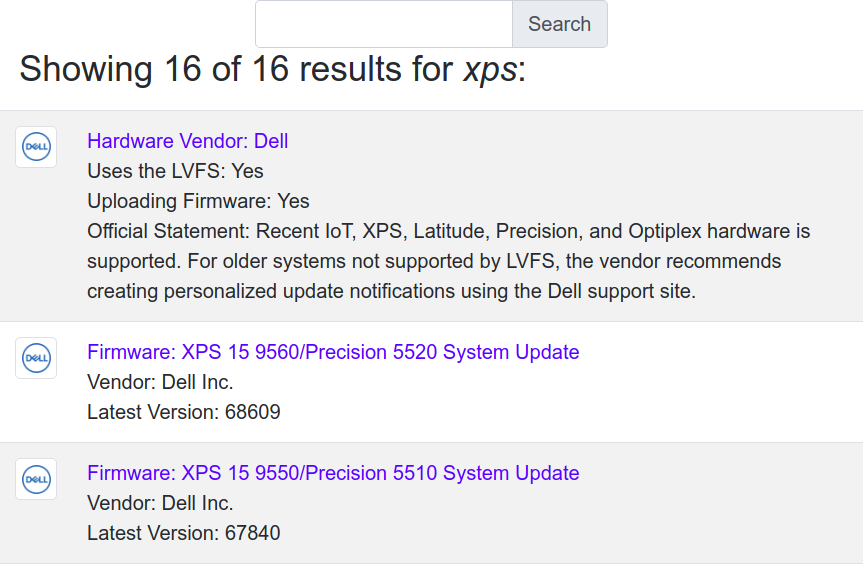
Search Using The LVFS
You can search for firmware and hardware vendors directly on the LVFS:
Using the D-Bus API
The fwupd daemon is launched when queried for the first time. This exports an interface that can be queried from any language with a D-Bus binding such as C, Python or Java.
$ gdbus call --system --dest org.freedesktop.fwupd --object-path / --method org.freedesktop.fwupd.GetDevices
({'5ad59b26d556e226f9e5e1ca13e4b717fe19802c':
'CHug-usb:00:01:04:04':
{'Guid': <'84f40464-9272-4ef7-9399-cd95f12da696'>,
'DisplayName': <'ColorHugALS'>,
'Version': <'4.0.0'>,
'Flags': <uint64 6>}},)
Do I always need the root password to update?
By default, any users are able to update signed firmware for removable hardware. The logic here is that if the hardware can be removed, it can easily be moved to a different device that the attacker owns. For non-removable devices only user accounts with administrative rights are able to update using firmware signed by the LVFS.
Administrative users (i.e. root) can install firmware that
does not originate from the LVFS (e.g. locally built) but fwupd does
not affect the separate secure boot requirements in any way.
Copyright © Linux Vendor Firmware Service Project a Series of LF Projects, LLC and its contributors with icons from Font Awesome. :: Project Charter :: Project terms of use and other policies